jairobel
GForum VIP
- Entrou
- Set 24, 2006
- Mensagens
- 13,098
- Gostos Recebidos
- 0
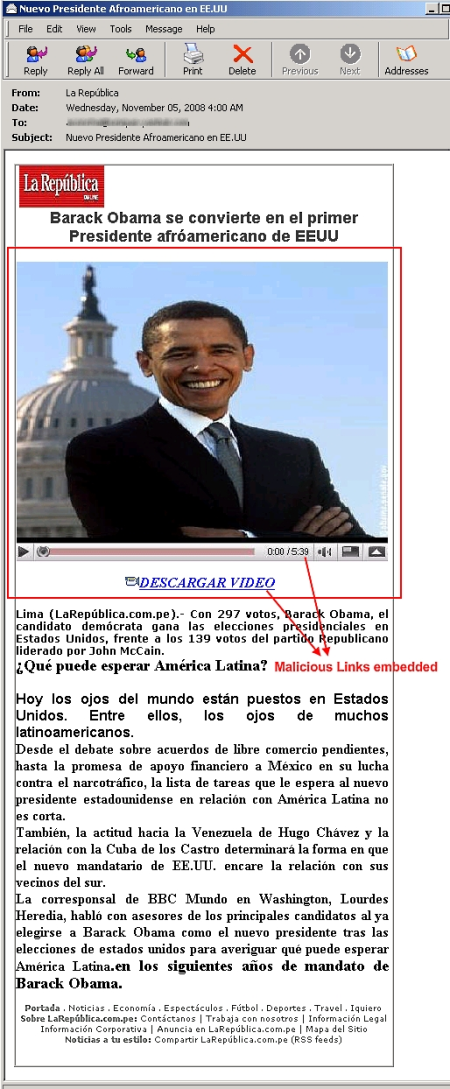
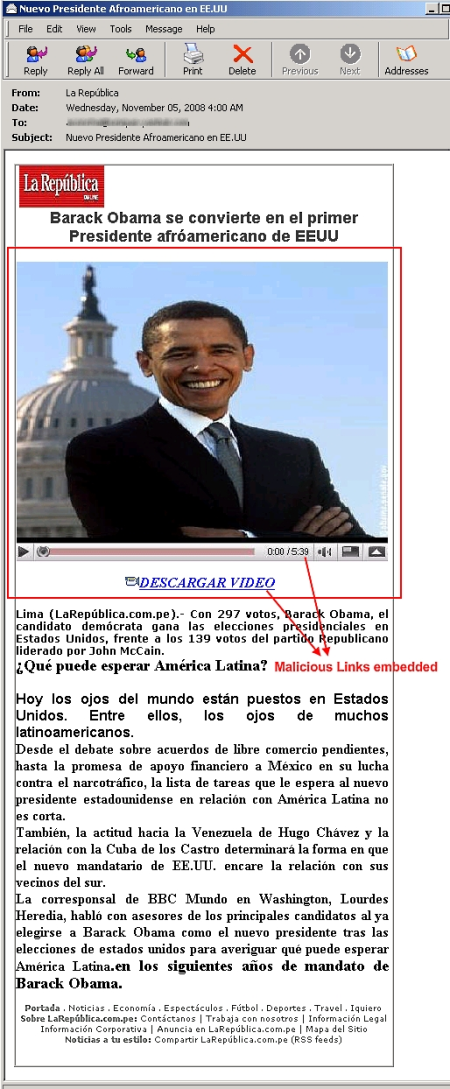
Barack Obama foi eleito presidente dos Estados Unidos... e já existe phishing sobre o fato. Circula um email em espanhol com um link para um vídeo que, para variar, esconde um cavalo-de-tróia. Fiquem de olho.
Alerts
BOOKMARK THIS ALERT
digg | del.icio.us | reddit
newsvine | furl | technorati US Presidential Malware - Barack Obama Interview Lure
Date:11.05.2008
Threat Type: Malicious Web Site / Malicious Code
Websense® Security Labs™ ThreatSeeker™ Network has discovered that malware authors are capitalizing on the recently announced results of the 2008 US Presidential election. Malicious email lures are being sent promising a video showing an interview with the advisors to the recently elected US President.
The email actually contains links to a file called 'BarackObama.exe' hosted on a compromised travel site at hxxp://*snip*.com/web/BarackObama.exe. This file is a Trojan Downloader with MD5 9720d70a5da9ca442ecf41e9269f5a27. Upon execution files called system.exe and firewall.exe are dropped into the system directory. A phishing kit is unpacked locally, and the dropped files are bound to startup. The hosts file is also modified.
Major anti-virus vendors are not detecting this Trojan Horse.
Alerts
BOOKMARK THIS ALERT
digg | del.icio.us | reddit
newsvine | furl | technorati US Presidential Malware - Barack Obama Interview Lure
Date:11.05.2008
Threat Type: Malicious Web Site / Malicious Code
Websense® Security Labs™ ThreatSeeker™ Network has discovered that malware authors are capitalizing on the recently announced results of the 2008 US Presidential election. Malicious email lures are being sent promising a video showing an interview with the advisors to the recently elected US President.
The email actually contains links to a file called 'BarackObama.exe' hosted on a compromised travel site at hxxp://*snip*.com/web/BarackObama.exe. This file is a Trojan Downloader with MD5 9720d70a5da9ca442ecf41e9269f5a27. Upon execution files called system.exe and firewall.exe are dropped into the system directory. A phishing kit is unpacked locally, and the dropped files are bound to startup. The hosts file is also modified.
Major anti-virus vendors are not detecting this Trojan Horse.

